Dive deep into the complex world of module injection, a devastating technique with the ability to manipulate application behavior. We'll investigate its mechanisms, uncovering the methods employed by both defenders and threat agents. From weak code analysis to cutting-edge mitigation approaches, this deep dive will empower you with the knowledge to
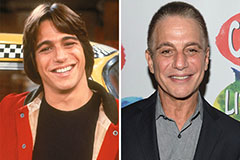 Tony Danza Then & Now!
Tony Danza Then & Now! Matilda Ledger Then & Now!
Matilda Ledger Then & Now! Lisa Whelchel Then & Now!
Lisa Whelchel Then & Now! Tonya Harding Then & Now!
Tonya Harding Then & Now! Jane Carrey Then & Now!
Jane Carrey Then & Now!